DATE
December 29, 2025
Most organizations think of cyber threats as something external. Phishing emails ransomware campaigns and attackers trying to force their way in. But many of the most damaging incidents never start with a breach.
They start with trusted access and no controls around what happens next.
An insider threat exists when someone inside an organization misuses legitimate access to systems or data in a way that creates risk. That person could be an employee a contractor a vendor or someone whose access was never fully removed.
What makes insider threats so difficult to manage is that nothing is broken into. The access is valid. The credentials work. The activity often looks routine.
For non-technical readers the idea is straightforward.
If someone is allowed to access sensitive information and that information is copied shared or removed in ways the organization did not intend there is insider risk regardless of intent.
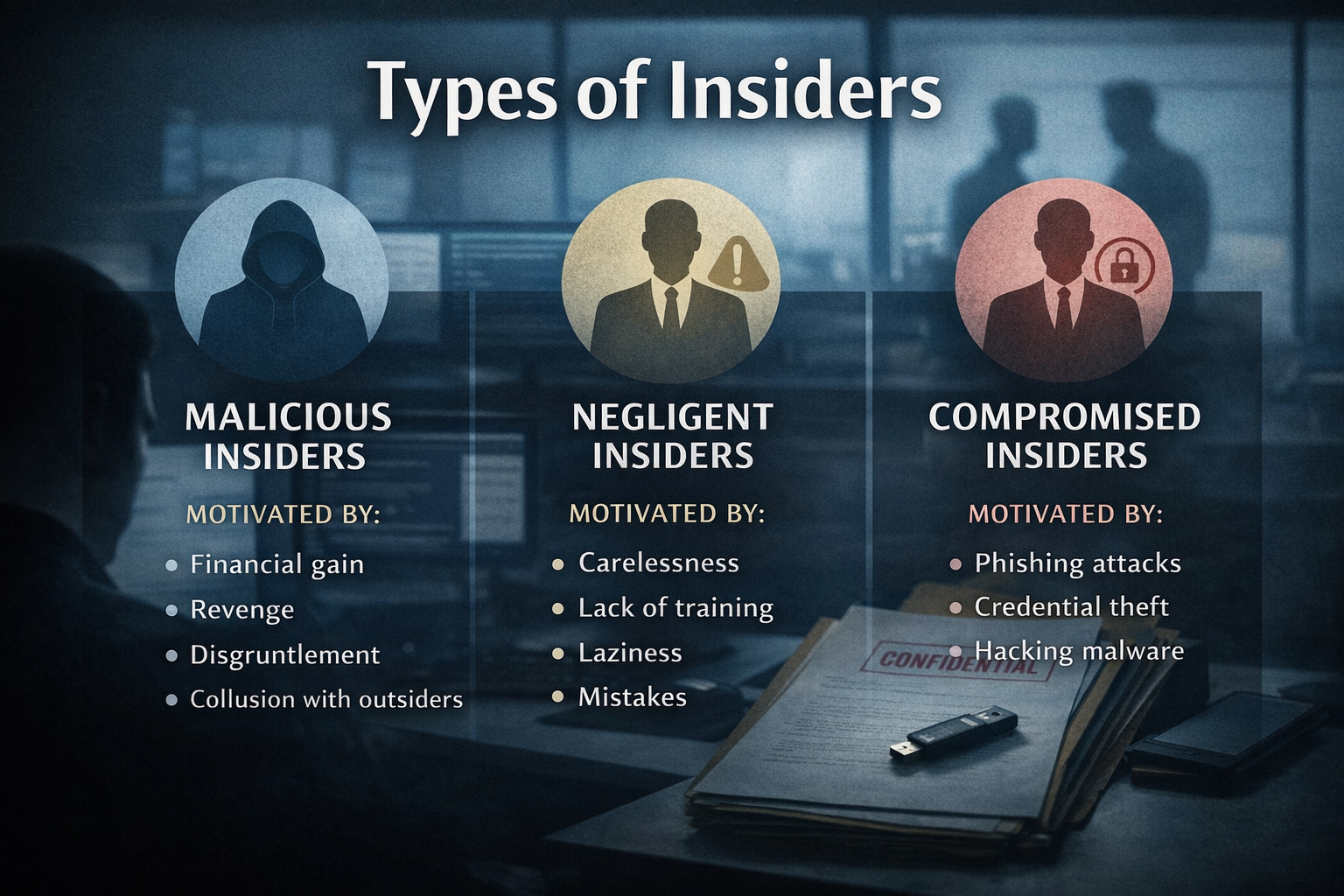
Insider threats typically fall into three patterns:
In all three cases the common factor is not who logged in but what happened to the data.
Modern threat actors are less interested in breaking systems and more interested in quietly extracting information.
Once inside an environment attackers can:
This is why insider access is so valuable and why organizations that focus only on perimeter security remain exposed.
Data Loss Prevention often sounds complex but the idea behind it is simple.
DLP focuses on how sensitive data is used and moved, not just who has permission to view it.
Instead of assuming authorized users will always handle information appropriately DLP introduces practical boundaries such as:
Without DLP organizations may know who has access but have little visibility into how sensitive data is actually handled day to day.
Traditional security controls are designed to stop outsiders. DLP assumes someone is already inside and asks how much damage they can realistically cause.
Without DLP organizations often miss:
With DLP in place organizations gain visibility into data movement patterns that would otherwise appear normal.
Effective DLP programs do not start with tools. They start with clarity and discipline.
Organizations should begin by:
Law firms and professional services organizations manage large volumes of sensitive information that constantly moves between people systems and clients.
Access is broad by necessity. That makes monitoring data movement, not just access, critical.
When insider incidents occur in these environments the impact often extends beyond technical damage into regulatory exposure client trust and long-term reputational harm.
Insider risk is often framed as a people problem or a security problem. In reality it is a data governance problem.
Organizations that understand where their sensitive data lives who can access it and how it is allowed to move are far better positioned to prevent misuse and demonstrate control when something goes wrong.
DLP is not about mistrust. It is about visibility accountability and defensible decision-making.
Insider threats are not rare and they are not always malicious. But the consequences are real and often avoidable.
Security programs that focus only on access leave a critical gap. Organizations must also manage what happens to data after access is granted.
At ikPin™ we help organizations reduce insider risk by aligning access governance monitoring and Data Loss Prevention into a single defensible security posture. Our compliance and advisory services are built to help firms prevent incidents and prove accountability when it matters most.
If you want help assessing insider risk or strengthening how sensitive data is controlled across your organization we are here to help.